Security Testing
MWSE's application security testing is a comprehensive assessment. It systematically checks the vulnerabilities of the application, source code and underlying infrastructure to achieve the highest level of assurance.
Our methodology is flexible to fit into diverse applications. Therefore each vulnerability assessment is unique depending on the client's requirements. We fine-tune our methodology to each specific environment to produce a better solution.
MWSE's application security testing methodology comprises of black box and or white box testing approaches. Further our methodology includes a source code review and an infrastructure configuration review
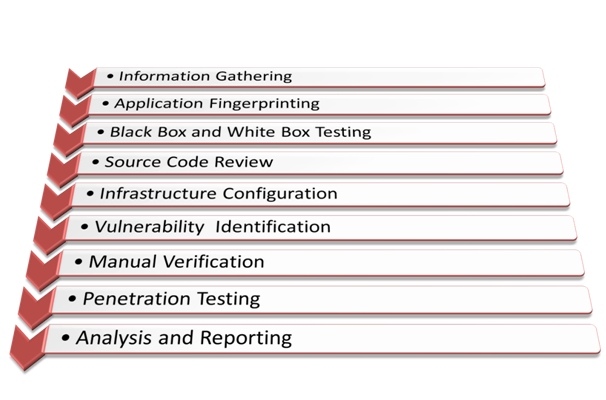
Our methodology consists of nine steps.
>> Information Gathering
This phase includes collecting information regarding the application. This information would be useful to map the imprtance of the application in terms of business. And this leads to which type of data the application would store , which type of security measures should the application implement . Further understand only relevant information is disclosed to the public
>> Application Fingerprinting
In application fingerprinting stage , we obtain information of which services are running on the application , what would be the underlying operating system and web server , which prtocols and programming languages are used , which are application entry points and understand web application logic and client side controls
>> Black Box and White Box Testing
Black box testing and or White box testing is carried out depending on client's requirement. This enables to analyse the information obtained from the above two phases. In both cases of testing different tests would be performed depending on the application in order to find out different vulnerabilities
>> Source Code Review
In this phase source code is reviewed for potential vulnerabilities. This is due to code may include vulnerabilities such as hardcoded back doors, potential information disclosure. This will lead to find the exact point where the vulnerability lies. Also potential vulnerabilities that could not be exposed by black box testing could be found
>> Infrastructure Configuration
In this stage current infrastructure configurations are reviewed for potential vulnerabilities. This includes configurations of the web server, Application server, Operating system, database systems
>> Vulnerability Identification
Black box and white box testing are carried out manually and or using automated tools. These tests result adverse vulnerabilities. In this phase we identify and present vulnerabilities of the web application, underlying infrastructure and source code. Eachvulnerability is assessed depending on the criticality on the vulnerability and reported immediately if necessary
>> Manual Verification
Even though automated tools are partially utilized for tests, Manual verification should be carried out on the test results to eliminate any false positives and false negatives
>> Penetration Testing
Based on the client's requirement MWSE would perform a proof of concept on identified vulnerabilities. During this stage unverified exploit code may be used. Hence client's consent is obtained prior to moving forward. However MWSE highly recommends not carrying out this stage on production servers due to it may lead to adverse outcomes
>> Analysis and Reporting
All the positing and negative findings are reported with recommendations for improvement. We use simple and clear explanations in our detailed reports to be understood by technical and management staff. All vulnerabilities are presents with a vulnerability rating to identify which should be attended first by the client